Your Checklist to Multi-State Privacy Impact Assessments
Master multi-state Privacy Impact Assessments by downloading this checklist.
An intuitive learning experience to transform the complexity of GDPR into simple and manageable actions.
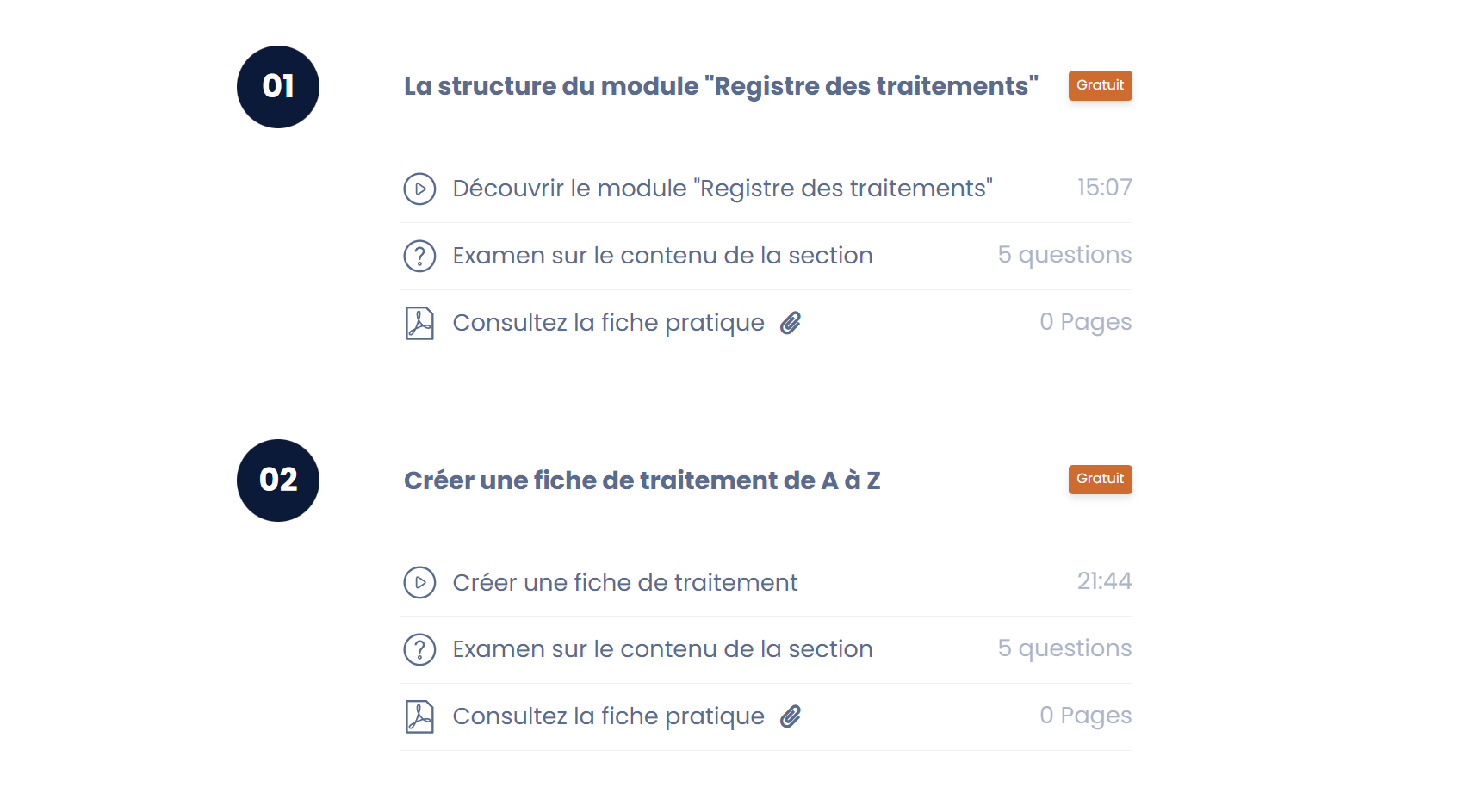
Learn to use Dastra at your own pace, challenge your knowledge, and certify your level through a comprehensive training course.
Find all the replays of Dastra Academy training sessions and learn at your own pace!
Visit the Dastra AcademyOur experts provide you with our free personal data processing models
Access the data processings library* You can unsubscribe at any time using the link provided in each newsletter.