What is a PIA ?
A Privacy Impact Assessment (PIA) - also referred to as a Privacy Risk Assessment under California’s CCPA/CPRA framework, or a Data Protection Assessment (DPA) under laws like the Colorado Privacy Act, or Data Protection Impact Assessment (DPIA) in Indiana - is a structured, documented risk assessment that an organization completes before starting a new personal data processing activity (or when materially changing an existing one).
Most states with comprehensive privacy laws follow "a baseline" model which requires a PIA when the processing activity is likely to result in a “significant” [CALIFORNIA] or “heightened” [ALL OTHER STATES] risk of harm to consumers.
There is no definition for those terms. Rather, privacy regulations often provide examples of such processing which generally includes (but is not limited to) **activities involving targeted advertising, profiling, sale of personal data, using new technologies & procsesing sensitive personal information (common state law triggers).**Some of them add a "catch-all" category like Indiana with similar wording "Any processing activities involving personal data that present a heightened risk of harm to consumers".
To help privacy teams navigate this complexity, we created several practical tools:
A multi-state PIA trigger questionnaire covering seven key U.S. privacy laws
A step-by-step PIA assessment questionnaire to conduct the assessment itself
A checklist for PIA best practices
Together, they provide a structured workflow for identifying and documenting high-risk processing activities.
Step 1: Identify when a PIA is required
Most U.S. privacy laws follow a similar logic: organizations must perform an assessment when processing activities present heightened risks to individuals.
Across the seven states included in our questionnaire, the most common triggers include:
Targeted advertising using cross-context targeting
Sale or sharing of personal data
Processing of sensitive personal data
Profiling that produces significant effects
Use of automated decision-making systems
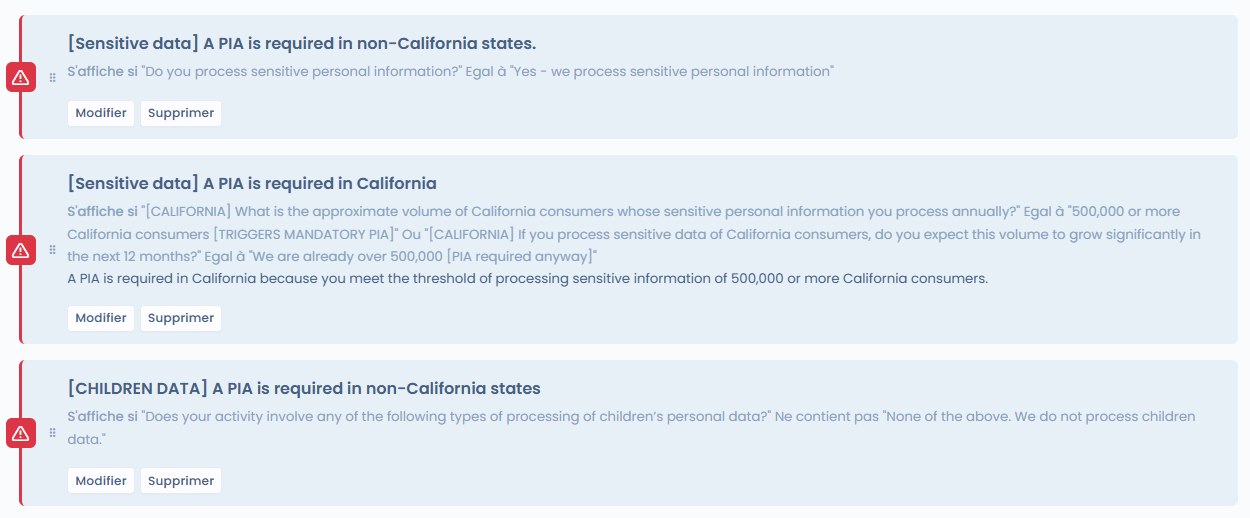
Using our pre-PIA questionnaire, instead of analyzing each law separately, teams can quickly identify whether an activity likely requires a PIA and move directly to the evaluation phase.By answering a short set of questions, you can quickly identify whether a PIA is likely required and which state laws may trigger the obligation.
Here’s a sneak peek of the questionnaire in action covering California, Colorado, Connecticut, Delaware, Indiana, New Jersey & Oregon:>
Best practice: Even if PIA are not required (ex Utah or Iowa), the use of PIAs is considered a best practice for organizations with a focus on protecting their clients’ or customers’ data and privacy interests. & generally a part of a better privacy governance.
When in doubt, conduct the PIA. The cost of non-compliance far exceeds the effort of a thorough assessment. A well-documented PIA demonstrates accountability and provides legal defensibility across several states.
Step 2: Conduct the Privacy Impact Assessment
Once a trigger is identified, organizations must perform the actual assessment.
A well-structured PIA should document several key elements:
1. Description of the processing & its context
Explain the activity clearly: the purpose of processing, the systems involved, and the business context.
2. Categories of personal data & individuals affected
Identify the types of personal data involved, including any sensitive data or special categories.
3. Proportionality of processing
Why processing is necessary, whether less intrusive alternatives exist & data minimization analysis.
4. Risk analysis
Evaluate potential risks to individuals, including privacy harms, discrimination, or misuse of data.
5. Benefits & balancing test
Weigh the benefits of processing (to controllers, consumers, and the public) against the risks to consumer rights, accounting for available safeguards.
5. Safeguards and mitigation measures
Describe the technical and organizational measures used to reduce risks.
5. Consumer rights & third party governance
Ensure consumer rights (access, rectification & many more) & third party governance.
6. Governance and accountability
Identify responsible stakeholders, review procedures, and escalation processes.
7. Documentation and evidence
Ensure the assessment is properly documented and available in case regulators request it.
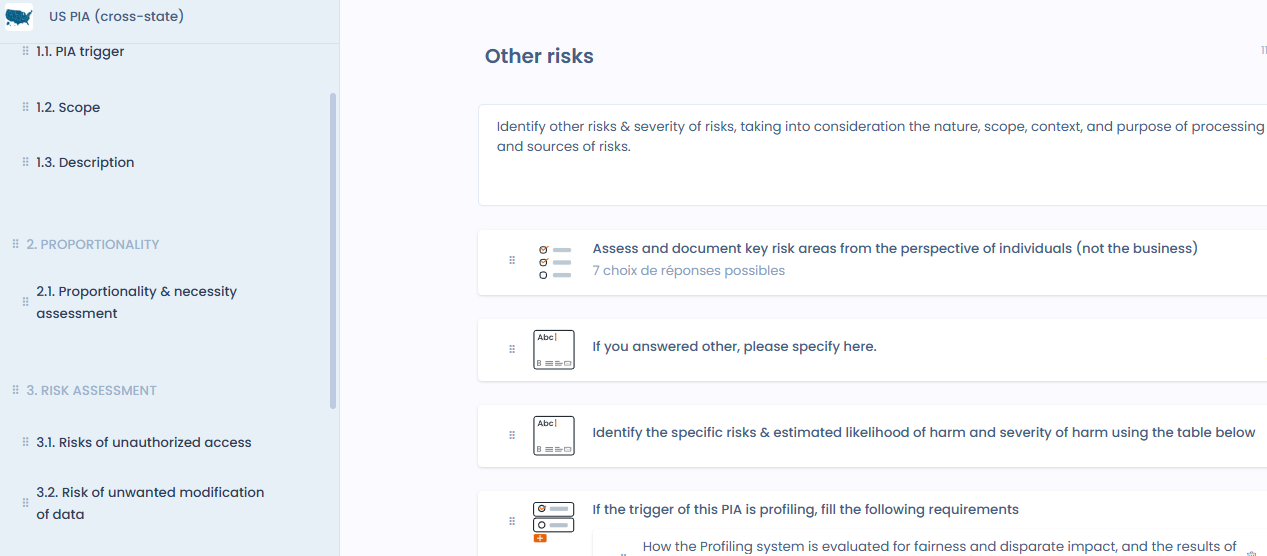
Our PIA questionnaire walks teams through each of these steps with the necessary details to ensure assessments are consistent, structured, and defensible.> > Here’s a sneak peek of how it works:
A smarter way to approach multi-state compliance
U.S. privacy compliance is evolving quickly. New state laws, regulations, and enforcement guidance continue to expand assessment obligations.
Rather than managing each law separately, privacy teams benefit from a more structured approach:
Screen processing activities for assessment triggers
Conduct standardized PIAs when required
Maintain documentation and evidence in one place
This helps organizations manage multi-state obligations more efficiently while maintaining strong governance over high-risk processing activities.